k8s使用ingress配置https
ingress是一个负载均衡应用,支持http和https,包括通过主机名的访问路径的过滤。通过ingress实现https访问的过程如下图所示: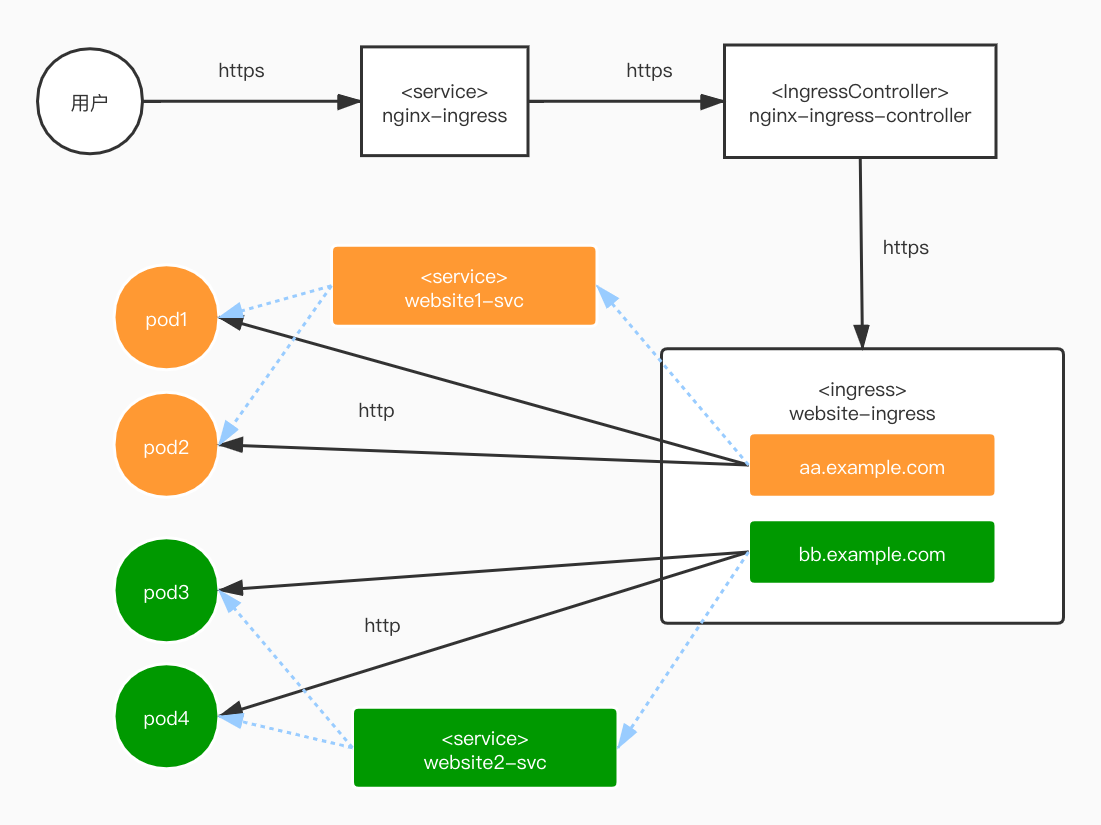
用户访问service是通过https,service向后端pod调度是通过http,这样就优化了集群,避免在每个pod上配置https,减轻的配置的负担和建立连接的压力。
部署
k8s的部署可以参考:使用kubeadm快速部署k8s
nginx-ingress的部署可以参考:k8s的ingress介绍和nginx-ingress的部署
ssl证书
这里是申请的阿里的一年免费证书: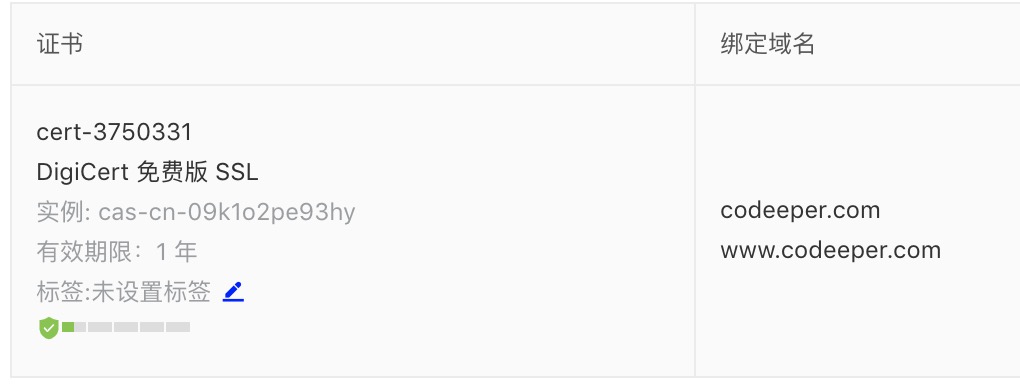
下载下来解压下来得到:
1 | root@codeeper:~# ls codeeper.com_nginx/ |
.key文件是私钥base64加密,.pem文件是证书base64加密。
部署一个后端nginx应用
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-rc
labels:
app: nginx
spec:
selector:
matchLabels:
app: nginx
replicas: 1
template:
metadata:
labels:
app: nginx
spec:
containers:
- name: nginx
image: registry.cn-shanghai.aliyuncs.com/lian_ns/nginx:1.19.2
ports:
- containerPort: 80
volumeMounts:
- name: nginx-conf
mountPath: "/etc/nginx/nginx.conf"
subPath: nginx.conf
- name: nginx-vhost-conf
mountPath: "/etc/nginx/conf.d/"
- name: nginx-www
mountPath: /var/www/
volumes:
- name: nginx-conf
configMap:
name: nginx-conf
- name: nginx-vhost-conf
configMap:
name: nginx-vhost-conf
- name: nginx-www
hostPath:
path: /opt/www/上面的一些字段说明暂且忽略,有一些需要说明
1
2
3
4
5
6
7
8
9
10
11
12
13
14volumeMounts:
nginx.conf的配置
- name: nginx-conf
mountPath: "/etc/nginx/nginx.conf"
subPath: nginx.conf
nginx虚拟主机配置文件目录的配置
- name: nginx-vhost-conf
mountPath: "/etc/nginx/conf.d/"
nginx网站目录的配置
- name: nginx-www
mountPath: /var/www/虚拟主机的配置
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16apiVersion: v1
kind: ConfigMap
metadata:
name: nginx-vhost-conf
data:
blog.conf: |-
server {
listen 80;
server_name www.codeeper.com codeeper.com;
charset utf-8;
location / {
root /var/www/blog;
index index.html index.htm;
}
}新建一个对上方deploy的service
1
2
3
4
5
6
7
8
9
10
11
12apiVersion: v1
kind: Service
metadata:
name: nginx-svc
spec:
ports:
- port: 80
targetPort: 80
protocol: TCP
name: http
selector:
app: nginx查看service
1
2root@codeeper:~# kubectl get svc | grep nginx-svc
nginx-svc ClusterIP 10.98.15.89 <none> 80/TCP 28h创建secret
可以使用yaml创建或命令行创建1
2
3
4
5
6
7
8
9apiVersion: v1
kind: Secret
metadata:
name: testsecret-tls
namespace: default
data:
tls.crt: base64 encoded cert
tls.key: base64 encoded key
type: kubernetes.io/tls由于tls.crt和tls.key的文件过大,这里使用命令行来创建。
1
kubectl create secret tls blog-tls-secret --key 3967376_codeeper.com.key --cert 3967376_codeeper.com.pem
查看secret
1
2
3
4
5
6
7
8
9
10
11
12root@codeeper:~# kubectl describe secret blog-tls-secret
Name: blog-tls-secret
Namespace: default
Labels: <none>
Annotations: <none>
Type: kubernetes.io/tls
Data
====
tls.crt: 3675 bytes
tls.key: 1675 bytes创建ingress
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: nginx-ing
annotations:
kubernetes.io/ingress.class: "nginx"
spec:
tls:
- hosts:
- codeeper.com
secretName: blog-tls-secret
rules:
- host: codeeper.com
http:
paths:
- path: /
backend:
serviceName: nginx-svc
servicePort: 80添加了
spec.tls字段,里面是用来配置https的。
浏览器访问验证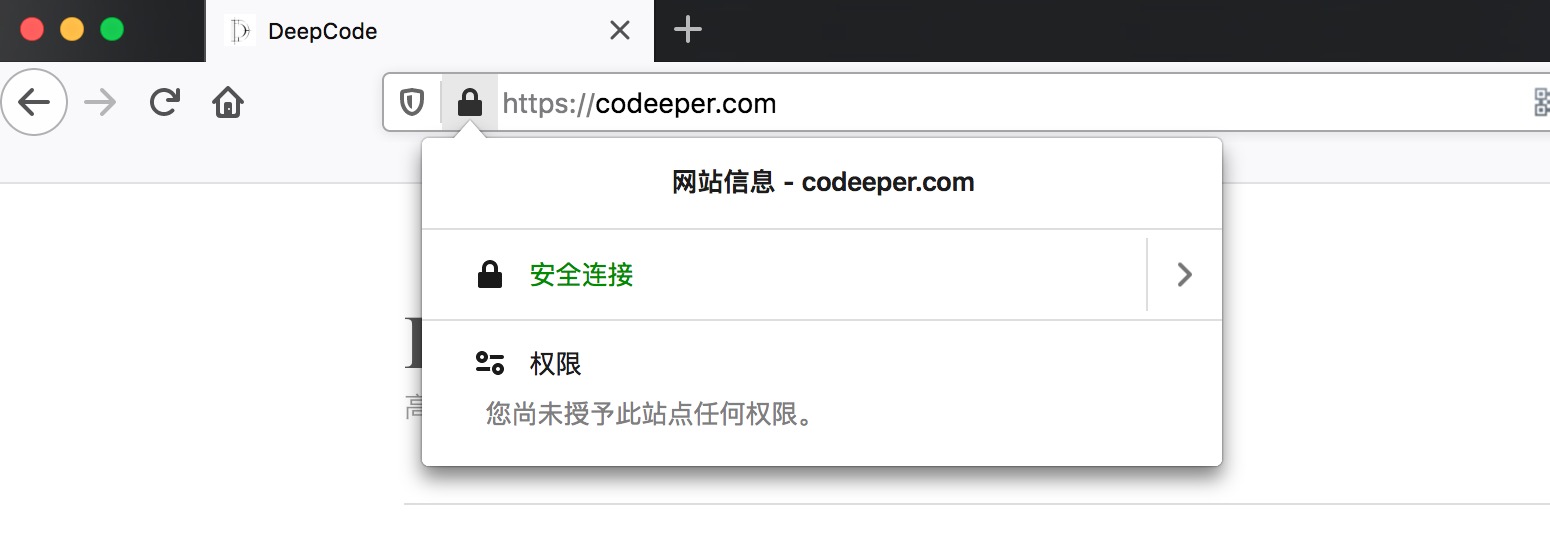
https部署的配置文件
https://github.com/dougaoyang/k8s_deploy
参考文档
https://kubernetes.io/zh/docs/concepts/services-networking/ingress/